Did you know that 93% of data breaches occur within minutes, yet 83% are not discovered for weeks?
This goes to show that your network security might seem robust, but hidden vulnerabilities can lurk within, posing significant risks. As Eric Woodard, CEO at Protek Support, says, “A chain is only as strong as its weakest link, and so is your network security.”
Understanding and mitigating these hidden threats is crucial to ensuring the security and integrity of your network. In this blog, we explore 13 types of hidden network security vulnerabilities you should be aware of to protect your organization’s network effectively.
13 Network Vulnerabilities That Could Put Your Business at Risk
1. Unpatched Software Vulnerabilities
Unpatched software is one of the most common network vulnerabilities. When software vendors release updates and patches, they often address known security flaws.
Failing to apply these updates promptly can leave your systems exposed to cyber attackers who exploit these vulnerabilities to gain unauthorized access.
Is Your Network Truly Secure?
Protek Support uncovers and addresses hidden vulnerabilities for complete protection.
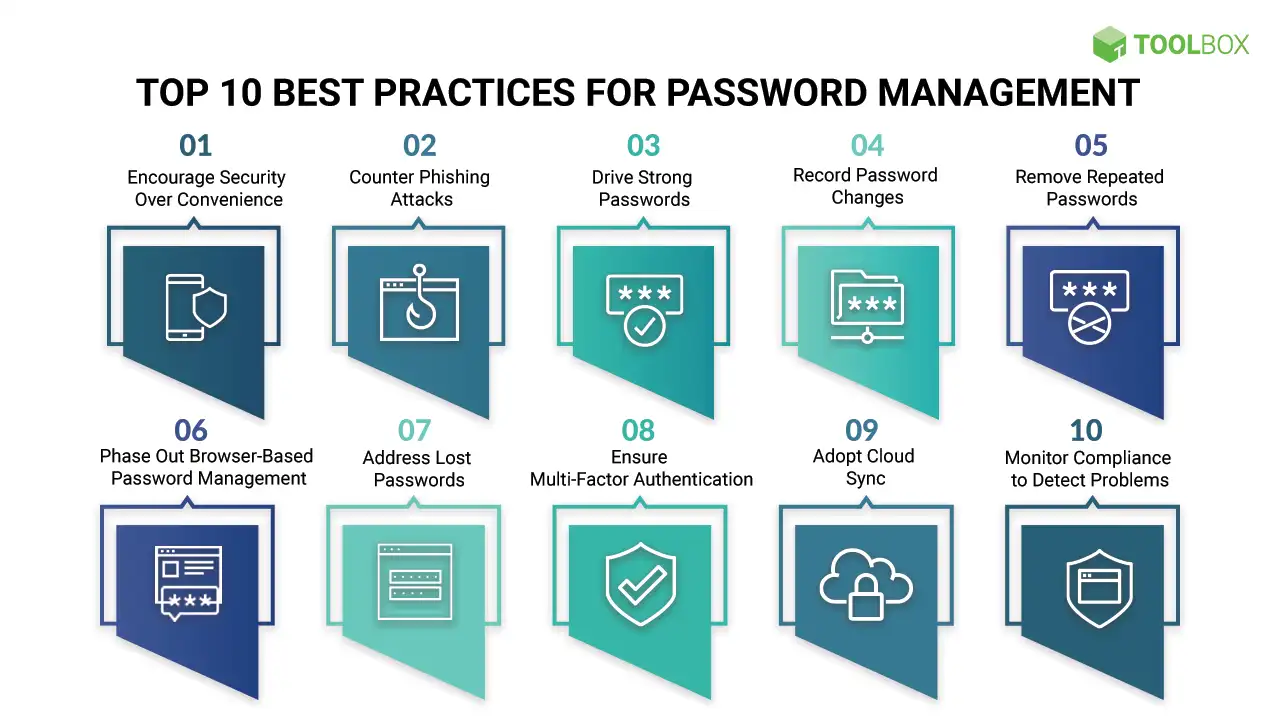
2. Weak Passwords and Lack of MFA
Weak passwords are a significant security risk. Using simple or easy-to-guess passwords can let hackers into important systems and data, says CloudSecureTech. Implementing strong password policies and multi-factor authentication (MFA) can significantly enhance security by adding an extra layer of protection.
Source: Spiceworks
3. Misconfigured Firewalls and Security Controls
Firewalls are essential for network security, but misconfigurations can create vulnerabilities. Research proves that 99% of firewall breaches are caused by misconfigurations, not flaws. Incorrectly configured firewalls can allow unauthorized access or fail to block malicious traffic. Regularly reviewing and updating firewall settings is crucial to maintaining a secure network.
4. Insecure Network Protocols
Using outdated or insecure network protocols can expose your network to cyber threats. Protocols like Telnet and FTP transmit data in plain text, making it easy for attackers to intercept sensitive information. Switching to secure protocols such as SSH and SFTP can mitigate this risk.
5. Insider Threats
60% of data breaches involve insiders, either through malicious intent or negligence. Employees with access to sensitive information can unintentionally or deliberately leak data. Implementing strict access controls and monitoring employee activity can help mitigate insider threats.
6. Social Engineering Attacks
Social engineering attacks manipulate individuals into divulging confidential information. Phishing emails and pretexting are common tactics used to deceive employees. Regular security training and awareness programs can help employees recognize and avoid social engineering attacks.
7. Lack of Network Segmentation
Network segmentation involves dividing a network into smaller, isolated segments. Without segmentation, a single compromised device can give attackers access to the entire network. Implementing network segmentation can limit the impact of a breach and contain potential threats.
8. Outdated Operating Systems
Using outdated operating systems exposes your network to known vulnerabilities that are no longer patched by vendors. Ensuring all systems run on supported and updated operating systems is critical to maintaining security.
| More resources you might like: |
9. Insufficient Physical Security
Physical security measures are often overlooked in network security strategies. Unauthorized physical access to network hardware can lead to data theft or system tampering. Implementing robust physical security measures, such as access controls and surveillance, is essential.
10. Inadequate Vulnerability Scanning and Penetration Testing
Regular vulnerability scanning and penetration testing are crucial for identifying and addressing security vulnerabilities. These practices help uncover hidden weaknesses before cyber attackers can exploit them. Integrating these tests into your security protocol can significantly enhance your network’s resilience.
11. Poor Access Control Management
Improper access control can allow unauthorized users to access sensitive information. Implementing strict access control policies and regularly reviewing permissions can prevent unauthorized access and protect critical data.
12. Lack of Employee Training
Employees are often the weakest link in network security. Lack of training can lead to unintentional security breaches. Regular training programs focused on cybersecurity best practices can empower employees to recognize and respond to potential threats.
13. Insufficient Monitoring and Logging
Without proper monitoring and logging, detecting and responding to security incidents becomes challenging. Implementing comprehensive monitoring solutions and maintaining detailed logs can help identify suspicious activities and respond promptly to potential threats.
Key Steps to Mitigate Network Security Vulnerabilities
| Step | Description | Recommended Tools/Practices |
| 1. Conduct Regular Security Audits | Regular audits help identify potential vulnerabilities before they can be exploited. | Use tools like Nessus or Qualys for automated vulnerability scanning. |
| 2. Implement Strong Encryption | Encrypt sensitive data both at rest and in transit to prevent unauthorized access. | Utilize SSL/TLS for data in transit and AES for data at rest. |
| 3. Enable Intrusion Detection Systems (IDS) | IDS can monitor network traffic for suspicious activity and alert administrators to potential threats. | Tools like Snort or Suricata can be used for IDS implementation. |
| 4. Conduct Employee Training on Cyber Hygiene | Educate employees on best practices for maintaining network security, such as recognizing phishing attempts. | Regular workshops and simulated phishing exercises can be effective. |
| 5. Develop an Incident Response Plan | Having a predefined plan helps ensure a quick and effective response to security incidents. | Follow frameworks like NIST or SANS for structured incident response planning. |
| 6. Use Network Access Control (NAC) | NAC solutions can enforce security policies on devices trying to access the network. | Implement tools like Cisco ISE or Aruba ClearPass for robust NAC. |
| 7. Keep Firmware and Drivers Updated | Ensure all network devices have the latest firmware and driver updates to mitigate known vulnerabilities. | Regularly check for updates from device manufacturers and automate updates where possible. |
| 8. Implement Zero Trust Architecture | Zero Trust principles ensure that no entity is trusted by default, enhancing overall security. | Use solutions like Microsoft Azure AD Conditional Access or Google BeyondCorp. |
| 9. Monitor Third-Party Integrations | Ensure that third-party applications and services comply with your security standards. | Conduct regular reviews and audits of third-party integrations. |
| 10. Regularly Backup Data | Regular backups ensure data can be restored in the event of a ransomware attack or data loss incident. | Use automated backup solutions and verify backup integrity periodically. |
Protect Your Network with Protek Support’s Expertise
Hidden network vulnerabilities can silently undermine your business, making it imperative to identify and address them promptly. Protecting your network goes beyond basic measures—it’s about staying ahead of potential threats.
| Discover Trusted Network Support Services Near You: |
Protek Support excels in delivering advanced network security solutions tailored to your specific needs. Our dedicated team leverages the latest technologies and strategies to ensure your network remains secure and resilient.
Don’t wait for a breach to take action. Contact us today to schedule a free consultation and fortify your defenses against unseen cyber threats. Let us help you secure your business’s future with our expert IT services.


