Cybersecurity risks have surged with the increase in remote work. As more people work from home, the vulnerabilities in our digital defenses have become glaringly apparent.
Research shows that 75% of IT professionals say their organizations are more vulnerable to cyberthreats now that they have switched to remote work.
As Eric Woodard, CEO at Protek Support, says, “Remote work’s rise demands a heightened focus on cybersecurity to safeguard sensitive data and operations.”
National Work From Home Day spotlights these challenges, urging businesses and individuals to prioritize security. Potential threats are everywhere, from unsecured Wi-Fi networks in coffee shops to personal devices lacking robust protection.
Addressing these risks is crucial to ensure the safety and productivity of remote workers. In this blog, we’ll explore essential cybersecurity tips to overcome the remote work challenges that many face today.
Remote Work Risks Keeping You Up?
Protek Support’s tailored solutions mitigate remote cybersecurity risks.
The Rise of Remote Work Challenges
Remote work presents unique cybersecurity risks that traditional office environments do not. Here are some key points to consider:
- Personal Devices: Research shows that 97% of respondents access work accounts on their personal devices, and 95% use them for work-related multifactor authentication. This creates unexpected vulnerabilities, as personal devices are now used to access sensitive company data.
- Public Wi-Fi Networks: Remote employees may work from various locations, such as coffee shops or shared spaces, where public Wi-Fi networks can pose significant threats.
- Lack of Physical Security: In a home or public setting, physical security measures present in an office environment, like secured access to the building, are absent.
- Inconsistent Security Policies: Ensuring all remote workers follow consistent security policies can be challenging, leading to potential vulnerabilities.
- Increased Attack Surface: Remote work’s diverse and distributed nature increases the number of potential entry points for cyberattacks.
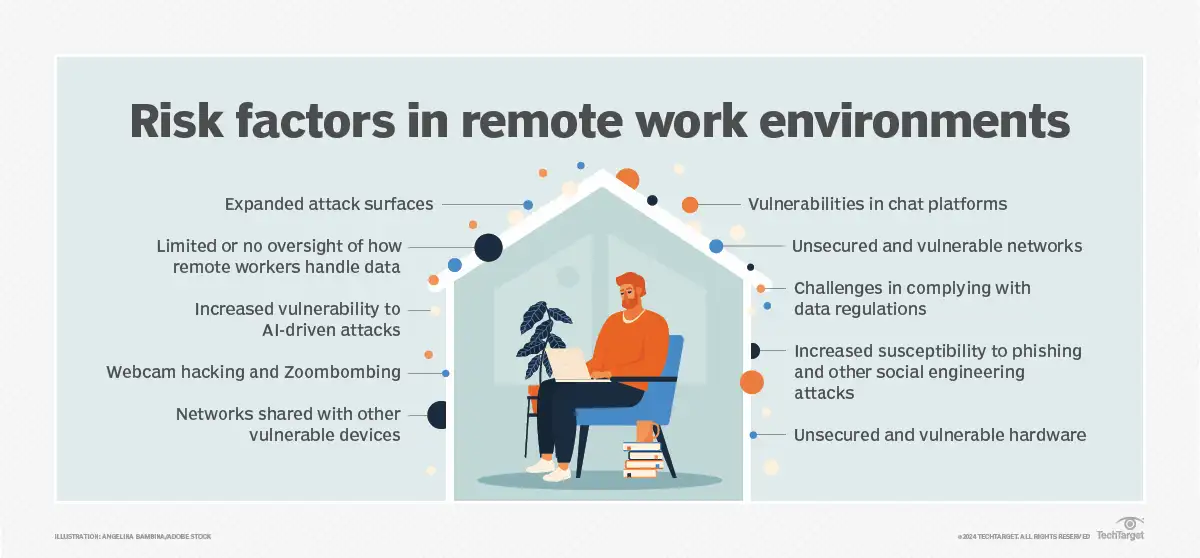
Source: TechTarget
Tips to Protect Your Business from Cyber Threats on National Work From Home Day
1. Implement Strong Password Management
One of the simplest yet most effective ways to secure remote work is through robust password management. Employees should use complex, unique passwords for different accounts and change them regularly.
Implementing multi-factor authentication (MFA) adds an extra layer of security. Password managers can help remote team members generate and store secure passwords, reducing the risk of unauthorized access.
2. Use Virtual Private Networks (VPNs)
A Virtual Private Network (VPN) encrypts internet connections, making it difficult for cybercriminals to intercept data.
Remote workers should always use a VPN when accessing company resources, especially on public Wi-Fi networks. This practice ensures that sensitive information remains secure, regardless of the remote working location.
3. Secure Collaboration Tools
Collaboration tools are essential for remote teams, enabling communication and project management across different time zones. However, these tools can also be vulnerable to cyberattacks.
Companies should choose collaboration tools with strong security features and regularly update them to protect against the latest threats. Employees should be trained to recognize phishing attempts and avoid clicking on suspicious links.
4. Implement Endpoint Security
Ensuring that all devices used for remote work are secure is critical. Endpoint security solutions, such as antivirus software and firewalls, should be installed on all devices.
Regular software updates and patches are necessary to protect against vulnerabilities. Companies should also have policies in place for securing personal devices used for work purposes.
| More resources you might like: |
5. Educate Employees on Cybersecurity Best Practices
95% of cybersecurity breaches are due to human error. Regular training and awareness programs can help remote employees recognize potential threats and respond appropriately.
Topics should include phishing, secure password practices, safe internet usage, and the importance of regular software updates.
6. Monitor Network Activity
Continuous monitoring of network activity can help identify unusual behavior that might indicate a security breach.
Advanced threat detection systems can alert IT teams to potential issues, allowing for swift action. Regular audits and security assessments can also help identify and mitigate vulnerabilities.
7. Promote a Secure Home Office Environment
Encouraging remote workers to create a secure home office environment is essential.
This includes using secure Wi-Fi networks, setting up strong router passwords, and ensuring that home networks are encrypted. Employees should also be advised to lock their screens when not in use and store sensitive documents securely.
Cybersecurity Tools for Remote Work
This table compares various cybersecurity tools and services that can help businesses address remote work challenges.
| Tool/Service | Description | Pros | Cons |
| Secure Email Gateways | Protects against email-based threats and phishing. | Real-time threat detection, user-friendly, integrates easily. | Can be expensive, and may require ongoing management. |
| Endpoint Detection and Response (EDR) | Monitors and responds to endpoint threats. | Comprehensive threat detection automated response capabilities. | High cost, requires skilled personnel for effective use. |
| Zero Trust Network Access (ZTNA) | Limits access to applications and data based on user verification. | Enhanced security granular control reduces insider threats. | Complexity in implementation, potential user experience issues. |
| Data Loss Prevention (DLP) | Prevents sensitive data from leaving the network. | Protects confidential information compliance enforcement. | Can be complex to configure, potential impact on performance. |
| Cloud Security Posture Management (CSPM) | Monitors cloud infrastructure for compliance and security risks. | Improves cloud security, automated monitoring, and compliance reporting. | Limited to cloud environments can generate false positives. |
| Identity and Access Management (IAM) | Manages user identities and access permissions. | Enhances security, simplifies user management, and supports compliance. | Complex implementation and ongoing maintenance are required. |
How Protek Support Can Enhance Your Cybersecurity
Remote work has become a double-edged sword. While it offers flexibility and improved work-life balance, it also exposes us to heightened cybersecurity risks. National Work From Home Day emphasizes the importance of addressing these risks head-on.
| Discover Trusted Cybersecurity Services Near You: |
Protek Support provides tailored solutions to help you navigate these challenges. Our expertise ensures that your remote teams remain secure and productive. Contact us today to schedule a free consultation and fortify your cybersecurity measures.


