From data breaches to cyberattacks, businesses and individuals alike face a myriad of threats on a daily basis. Network security serves as the first line of defense, safeguarding sensitive data and ensuring seamless operation. But what exactly is network security and what are the main network security types that everyone should know about?
“Neglecting network security is akin to driving without wearing a seatbelt on a busy highway – it’s not a question of if, but when an accident will occur. Our duty is to ensure that you are always protected and prepared to navigate the digital landscape securely,” says Eric Woodard, CEO of Protek.
In this blog post, we’ll delve into the importance of digital protection, uncovering the various types of network security, such as firewall, Intrusion Detection System (IDS), Virtual Private Networks (VPN), as well as the different types of scanning in network security.
The Importance of Network Security
Before getting into the different types of network security, it’s vital to understand how important network security is today to protecting your business.
Network security is a widely adopted concept that includes a range of strategies and techniques aimed at protecting network and data integrity, safety, and usability. In providing network security solutions, managed IT providers or managed security providers play a pivotal role in preventing unauthorized access to computer networks and their resources.
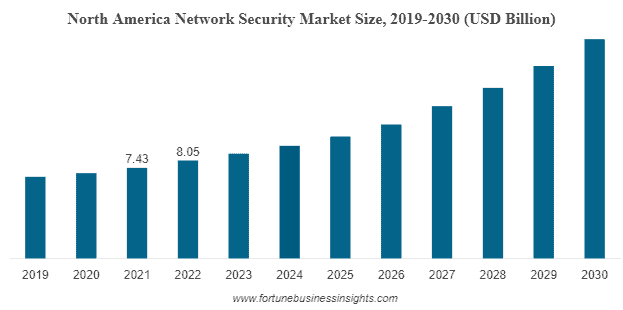
Image Credit: Fortune Business Insights
According to a report, the world-wide network security market size was USD 23.66 billion in 2021 and is projected to reach USD 54.13 billion by 2028, exhibiting a CAGR of 12.12%.
There has been an upsurge in the demand for network security services in recent years due to the increasing recognition of network security’s critical role in safeguarding a business’s digital assets. For businesses of all sizes and sectors, network security is not just a ‘nice-to-have,’ but a ‘must-have,’ providing the foundation for digital safety.
But what types of network security are most essential to your business? Let’s take a look.
9 Different Types of Network Security You Should Consider
1. Firewalls
The quintessential first line of defense when examining the different types of network security is firewalls. Firewalls act as a barrier between trusted internal networks and untrusted external networks such as the internet. They use defined rules to allow or block traffic.
2. Intrusion Prevention Systems (IPS)
These systems identify fast-spreading threats, such as network worms, and prevent them from gaining access to the network. IPS technologies can also detect and block attacks from hackers. Curious to learn more? Check out these additional resources to learn more about the different network security types in our all-in-one cyber checklist!
| Resources: |
3. Network Scanning
Network scanning is a vital step in network security that helps identify active hosts (devices) on a network and the services they offer. In order to enhance the level of security, it provides a thorough insight into any potential weaknesses or threats.
Various types of scanning in network security include port scanning to find open ports, network mapping to understand the network’s architecture, vulnerability scanning for known weaknesses, and IP scanning to detect active IP addresses in a network.
4. Anti-virus and Anti-malware Software
Anti-virus and anti-malware software are used for detecting, preventing, and removing viruses and malware like worms, Trojans, ransomware, and spyware. Even after the initial detection, this software continues to protect by scanning and removing threats.
5. Virtual Private Networks (VPNs)
VPNs provide a secure connection for remote users to access your network. By creating a “tunnel” through the internet, VPNs encrypt data from the user’s device to the network, making it difficult for hackers to breach.
6. Data Loss Prevention (DLP) Technologies
These network security technologies prevent end-users from sending sensitive data outside the network. Companies can use DLP to ensure employees don’t send sensitive information to outside networks intentionally or unintentionally.
Did You Know a Data Center Outage Can Cost Up to $7,900 Per Minute?
Stay Safe with Protek
7. Network Access Control (NAC)
NAC solutions help companies control access to their networks based on specific policies, like user role or device type. This type of network security can block non-compliant devices or give them only limited access.
8. Email Security
Given that emails are a common gateway for threats, email security solutions can block incoming attacks and control outbound messages to prevent data loss. According to PR Newswire, the global email security software market is to reach 1.3 billion by 2026 alone.
9. Encryption
Encryption transforms readable data into a coded form, so it can only be read or processed after it’s been decrypted. There are various types of encryption in network security, and they are all essential for protecting sensitive data, particularly when it’s being transferred across networks, safeguarding it from potential interceptors.
Among some of the common types of encryption in network security include symmetric encryption, asymmetric encryption, and more.
Don’t Leave Your Network to Chance: Protect Your Business with Protek
Protect Your Network with Protek
Protek understands that network security isn’t just about technology; it’s about safeguarding your business with peace of mind. With 11+ years of experience, a deep understanding of the ever-evolving threat landscape, and a comprehensive suite of network security services, we’re committed to protecting your data as if it were our own.
Our expertise spans the full spectrum of network security, from firewalls to VPNs, ensuring your digital assets remain secure and your operations uninterrupted. And our track record speaks for itself: a legion of satisfied clients who trust us with their network security, and a significantly safer digital landscape as a result.
Choose Protek for your network support and join us on the journey to a more secure digital world. Your security is our priority – contact us today!
