Cyber threats and data breaches pose significant risks, underscoring the need for strong information security practices in today’s business environment. One essential tool for fortifying your digital defenses is an information security policy.
Acting as a guiding framework, an information security policy establishes guidelines and promotes a culture of security awareness within an organization. As the CEO of Protek Support, Eric Woodard, says, “In today’s digital landscape, the importance of data security is non-negotiable. Following a proven IT Security framework is a necessity.”
In this blog post, we will explore the significance of information security policies, their benefits, and why every organization should have one in place.
Information Security Policies: A Breakdown
What is an information security policy?
An information security policy is a comprehensive set of guidelines and procedures designed to protect an organization’s sensitive information and digital assets from unauthorized access, theft, and damage. Today, where cyber attacks are on the rise at an alarming rate and almost 43% are targeted at SMBs, information security policies are more essential than ever before.
According to a recent report, it is estimated that cybercrime will cost the world $10.5 trillion annually by 2025, highlighting the urgency and severity of the situation. These attacks can result in financial losses, reputational damage, legal repercussions, and the compromise of sensitive customer data.
By having a well-defined information security policy template in place, your organization can proactively mitigate risks, enhance your resilience against cyber threats, and demonstrate your commitment to protecting both your own interests and the trust of your customers.
Let’s take a look at some examples of sample information security policy templates.
Information Security Policy Template Examples: What Needs to Be Included?
The cyber security market is projected to soar from $172.32 billion in 2023 to $424.97 billion in 2030.
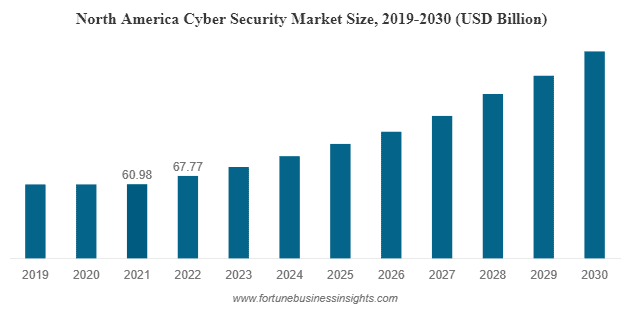
Image Credit: Fortune Business Insights
Information security policies are becoming more prevalent as cybersecurity becomes more sophisticated. When it comes to creating an information security policy, there are various sample information security policy templates available that can serve as a useful starting point.
Perfect Your Information Security Policy with Protek Support
Learn more about how we can help fortify your digital defenses
These information security policy examples typically cover essential areas of information security and can be tailored to meet the specific needs of an organization. A comprehensive information security template for small businesses should include:
- Introduction and Purpose: The introduction and purpose section outlines the purpose of the information security policy, sets the context for security requirements within the organization, and defines the scope and applicability of the policy.
- Information Classification: Here, your organization identifies different categories of information they handle and establish criterium for classifying and protecting sensitive data based on its level of confidentiality, integrity, and availability.
- Roles and Responsibilities: This section defines the roles and responsibilities of individuals within your organization regarding information security, including management, employees, and IT personnel, clarifying specific security standards and obligations and accountability measures.
- Access Controls: This component of the policy outlines measures for controlling access to information systems and data, including authentication mechanisms, password policies, user account management, and authorization processes.
- Data Handling and Storage: This aspect requires your organization to define guidelines for proper data handling, storage, and disposal, including encryption requirements, backup procedures, physical security measures, and secure disposal practices.
| What is the information security policy’s role in protecting your business? Inquire with our experts today: |
- Incident Response: All effective information security programs include procedures for reporting and responding to security incidents, including incident identification, escalation, investigation, containment, and communication protocols.
- Acceptable Use and Security Awareness: This section covers guidelines on acceptable use of company resources, including computers, networks, and internet access, as well as security awareness training programs to educate employees about potential risks and best practices.
- Compliance and Monitoring: Your business should address legal and regulatory requirements specific to their industry and establish mechanisms for monitoring and auditing compliance with the information security policy, such as regular security assessments and reviews.
Remember, these are just some of the components that are typically included in information security policy examples. For optimal protection, you should customize the information security template for your small business to align with your unique needs, industry regulations, and the specific risks you face.
Regular reviews and updates to the policy are also essential to adapt to changing threats and technology landscapes, ensuring that information security remains robust and effective over time.
| Check out these additional resources to learn more: |

Perfect Your Information Security Policy Strategy with Expert Support from Protek
Now comes the decision of who to outsource your information security policy project to. Why choose Protek Support?
We offer specialized expertise and experience in developing and implementing comprehensive information security policies customized to your specific business requirements. We can help you align your policy with industry best practices, regulatory compliance, and evolving threat landscapes using our knowledge and resources.
With Protek Support as your partner, you can focus on your core business activities, knowing that your information security is in capable hands. Don’t leave your valuable data vulnerable to cyber security threats – entrust it to the experts at Protek Support and safeguard your organization’s future. Contact us now!


